GDPR & Europe
GDPR Compliant Data Erasure Software
NIST 800-88 certified erasure for Article 17 right to be forgotten and Article 5 storage limitation. Built for European organizations.
The Problem
OS-level "delete" is not GDPR Article 17 compliant.
GDPR mandates erasure of personal data "without undue delay" (Article 17). Standard OS-level delete, quick format, and "moving to trash" do not constitute genuine erasure — they can be recovered with basic tools. Article 5(1)(e) Storage Limitation Principle requires erasure once retention period expires. In an audit, "we deleted it" must be backed by documentation.
Fines Up to €20M
Article 83 imposes up to 4% of annual revenue or €20M, whichever is higher.
Storage Limitation
Article 5(1)(e): data must be erased once purpose is met. Legacy backup disks, unused laptops are typical violation sources.
Burden of Proof
Under GDPR, the controller bears the burden of proof. "We deleted it" without certification fails in an audit.
GDPR Articles & PIWIPE
How PIWIPE addresses GDPR articles
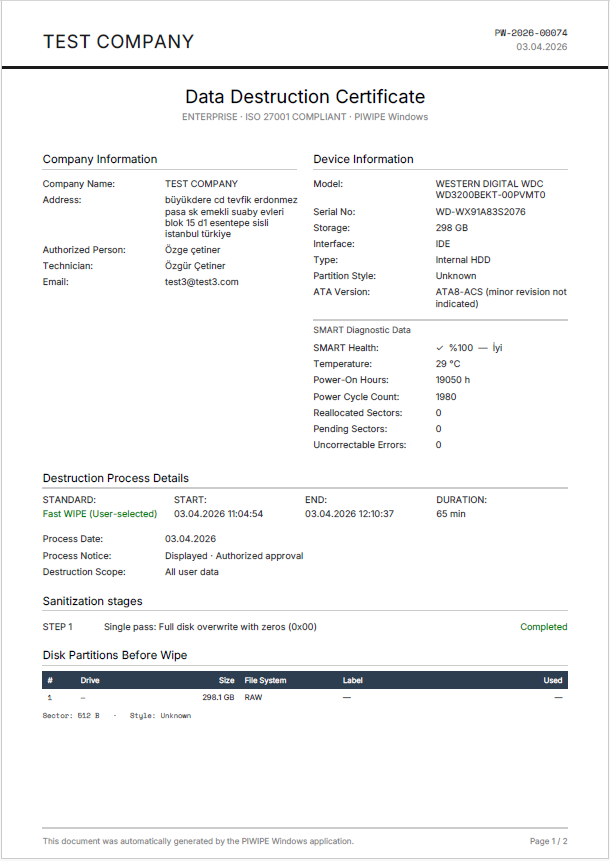
When a data subject requests erasure, data must be removed from both production systems and backup/archive media. PIWIPE sanitizes decommissioned backup disks via NIST 800-88 and produces a verifiable certificate per device. The cloud console archive can be presented to a data subject or DPA via QR on audit request.
A systematic process is required to erase personal data once retention expires. PIWIPE integrates into IT refresh, laptop inventory, and mobile rotation workflows for automated certified erasure. Each certificate carries device serial, method used, and SHA-256 hash.
Article 32 requires risk and security controls including the "destruction" scenario. Certified erasure is the implementation of this control at the end of the hardware lifecycle. PIWIPE's 5 standards (NIST, DoD, NVMe Sanitize, etc.) give flexibility per your risk assessment.
ISO 27001 ISMS control A.8.10 "Information Deletion" and ISO 27040 storage security provide reference frameworks for hardware destruction. PIWIPE fulfills these controls with certificates and audit trail; used as direct evidence in internal audit reports of ISO 27001-certified organizations.
DPA-Ready
Records ready for the Data Protection Authority
Each certificate has 3-layer verification: SHA-256 hash, PKCS#7 digital signature, and QR-linked public verification — no login needed.
Data Subject Access
Provide QR-verifiable certificate on Article 17 request.
DPA Audit
Bulk certificate export for delivery to data protection board.
EU Data Residency
Cloud console can be hosted on EU servers (optional).
Chain Integrity
SHA-256 hash + digital signature detect any tampering.
Use Cases
PIWIPE across the GDPR lifecycle
From banking to e-commerce, HR offboarding to post-breach control — concrete scenarios for European organizations.
Banking — Data Subject Request
When a customer files an Article 17 erasure request, document copies may exist on multiple disks. PIWIPE locates the relevant inventory and sanitizes it; QR-verifiable certificates are delivered within the one-month response window.
E-Commerce — Retention Limit
Order history and payment data have legal retention limits. PIWIPE's periodic inventory mode scans legacy backups against the retention table; expired media is flagged for sanitize and Article 5(1)(e) is satisfied.
HR Offboarding
Departing employees' laptops, phones, and USBs retain HR and special-category data. Integrate PIWIPE into offboarding — laptop NIST 800-88 Purge, phone Knox/Apple Erase All, certificate filed in the personnel record.
Post-Breach Containment
After the Article 33 72-hour notification, all relevant hardware is sanitized and certified as a containment measure. The DPA-bound report is generated directly from the PIWIPE archive.
IT Refresh & ITAD
Devices retired on three-year cycles are sanitized via PIWIPE before handover to an ITAD partner. Cloud archive plus ITAD certificate provides dual verification; the chain-of-custody removes breach risk.
Legacy Backup Tape & USB Archive
Backup archives 5+ years old in a data centre corner may still hold EU citizen data. PIWIPE supports legacy interfaces (SCSI, eSATA, USB-A) and produces bulk sanitize certificates.
Other frameworks: NIST 800-88 · HIPAA · KVKK
Compliance Checklist
GDPR data erasure audit checklist
A 9-item checklist based on Articles 5, 17, 30, 32, and 33. Controls PIWIPE directly fulfills are (✓); items requiring your written policy are (◐).
- ✓Personal Data Inventory — Article 30 records of processing; PIWIPE logs serial/type for every connected device.
- ✓Retention Table — Define retention per data category; PIWIPE periodic scan matches against this table. (◐)
- ✓NIST 800-88 Implementation — Article 32 "appropriate technical measure"; PIWIPE selects Clear/Purge level per device.
- ✓Data Subject Request Workflow — One-month response (Article 12); PIWIPE workflow log tracks the deadline.
- ✓Tamper-Proof Certificate Generation — SHA-256 + PKCS#7 signature; independent per-device verification.
- ✓EU Data Residency (optional) — Cloud console can be hosted on EU servers; SCC/transfer assessment available.
- ✓DPA-Ready Access — Bulk PDF/CSV export; QR public verification.
- ✓DPIA / TIA Document — Article 35 impact assessment for high-risk processing; PIWIPE deployment template provided. (◐)
- ✓Breach Notification Readiness — For Article 33 72-hour response, the wipe certificate is the basis of a "no risk" assessment.
Frequently Asked
GDPR & Data Erasure
EU Data Residency
After Schrems II: keep certificates in the EU or on your own server
GDPR Articles 44-49 restrict transfers of personal data to inadequate-protection countries. After Schrems II (C-311/18), Standard Contractual Clauses alone are insufficient for U.S. transfers — a Transfer Impact Assessment and supplementary technical measures are required. Since certificates contain PII (device serial, operator email, customer name), storing them on a foreign cloud may be challenged by the DPA as a questionable transfer.
PIWIPE writes each certificate to the FTP/SFTP server you designate — this can be your EU data center (Frankfurt, Amsterdam, Paris, Dublin), a GDPR-certified EU cloud provider (OVH, Hetzner, Scaleway), or your own office. Sync to the PIWIPE cloud console is optional and can be disabled; in that case certificates containing personal data never cross EU borders, eliminating the Article 44 transfer regime entirely. Comparison page →
Close the GDPR lifecycle with PIWIPE.
Demo and pricing on request.
Or call us: +90 212 916 12 22