Healthcare & HIPAA
HIPAA Compliant Disk Wipe Software
NIST SP 800-88 certified PHI sanitization — HDDs, SSDs, NVMe, USB drives, and mobile devices. Tamper-proof PDF certificates with QR verification. Built for healthcare.
The Problem
Formatting is not enough under HIPAA.
HIPAA Security Rule §164.310(d)(2)(i) requires controlled disposal of all electronic media containing Protected Health Information (PHI). Standard OS-level delete, quick format, and repartition do not permanently destroy data — they can be recovered with free recovery tools. On SSDs, wear-leveling and over-provisioning make the situation even more complex.
Heavy Fines
HIPAA violations carry $100–$50,000 per violation, with an annual cap up to $1.5M. PHI leakage from decommissioned devices is a typical breach scenario.
Documentation Mandate
HIPAA mandates retention of disposal records for PHI-containing devices for 6 years. A vague "we ran format" statement is insufficient for an audit.
SSD Complexity
On SSDs, wear-leveling spreads writes across physical cells. Single-pass software wipes can leave PHI in spare cells. Hardware-level sanitize is required.
Standards Mapping
How PIWIPE meets HIPAA requirements
HIPAA Security Rule §164.310(d)(2)(i): "Implement policies and procedures to address the final disposition of electronic protected health information and the hardware or electronic media on which it is stored." HHS guidance cites NIST SP 800-88 as the reference for this control. PIWIPE records on the certificate the method, pass count, and verification result for every wipe.
NIST 800-88 defines three levels by media type: Clear (software-based overwrite, protects against logical recovery), Purge (protects against advanced laboratory techniques — degauss or cryptographic erase), and Destroy (physical destruction). PIWIPE covers Clear and Purge for modern HDDs; for SSDs it provides hardware-level Purge via NVMe Sanitize and ATA Secure Erase.
Some healthcare organizations prefer 3-pass sanitization due to internal policy. PIWIPE applies DoD 5220.22-M with 0x00, 0xFF, and random pattern per pass + sector verification. Note: HIPAA does not directly require this; it is chosen based on internal risk policy.
The NVMe Sanitize command is issued directly to the SSD controller; all NAND flash including over-provisioning regions and hidden cells is purged. Software-level recovery becomes impossible. PIWIPE automatically falls back to NIST 800-88 Purge for unsupported drives and records on the certificate which method ran.
PHI-Containing Media
For every media type you encounter in healthcare
From EMR/EHR server drives to staff smartphones; from diagnostic device storage to legacy backup USBs, PIWIPE sanitizes every PHI-containing device from a single console.
HDD
SATA / IDE / SAS
SSD
SATA / NVMe / M.2
USB Flash
Removable Storage
Android
Smartphones & Tablets
iPhone / iPad
iOS Devices
Memory Cards
SD / microSD / CF
Servers
RAID / Multi-Disk
Medical Devices
Removable Storage
Auditable Certificate
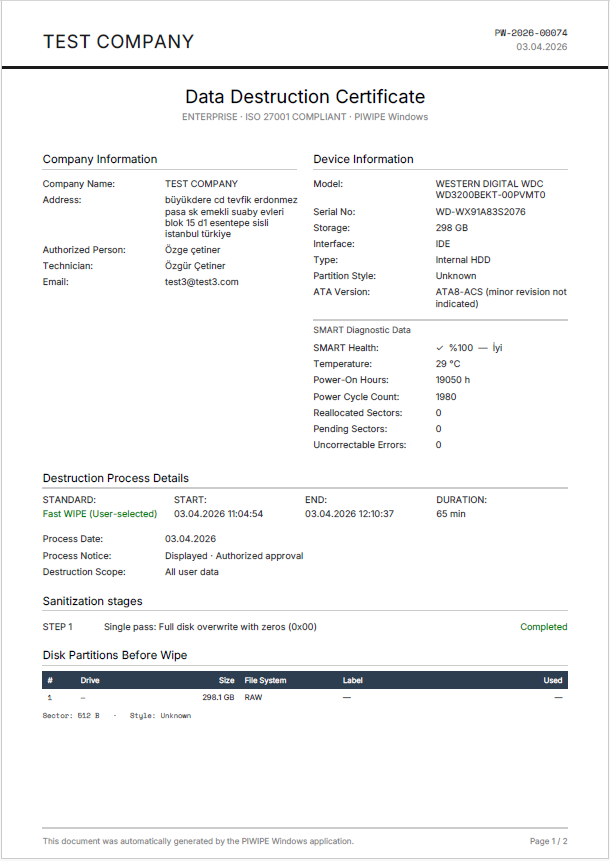
A document trail for 6-year HIPAA retention
After each wipe PIWIPE produces a certificate with three-layer verification: SHA-256 integrity hash, PKCS#7 digital signature, and a QR-linked public verification page.
Device Identity
Brand, model, serial number, IMEI, capacity, S.M.A.R.T. health data.
Sanitization Method
NIST 800-88 / DoD / NVMe Sanitize, pass count, verification result.
Operator and Date
Technician who performed the wipe, start/end timestamp, duration.
Independent Verification
Public verification page via QR — auditor can access without login.
Workflow
Four-step process for healthcare
Inventory
Connect decommissioned medical devices, server drives, and mobile devices to the PIWIPE console.
Select Standard
NIST 800-88 (recommended), DoD 5220.22-M, or NVMe Sanitize, per organizational policy.
Wipe + Verify
Parallel multi-wipe; each sector overwritten and verified. Failed devices are flagged.
Certificate Archive
PDF certificates auto-upload to the cloud console. Search, filter, and bulk export for 6-year retention.
Use Cases
PIWIPE across the healthcare ecosystem
From hospital server rooms to clinic laptops, medical devices to insurance offices — HIPAA requirement is the same, devices vary.
Hospital EHR Server
Decommissioned RAID disks from Epic, Cerner, or in-house EHR servers. NVMe Sanitize + per-disk certificate; chain-of-custody enters the compliance officer's audit folder.
Clinic Laptop Refresh
Physician/nurse laptops cycle every three years; legacy SSDs hold notes and patient imagery. Certified NIST 800-88 Purge erasure; clean handover to next device.
Staff Phone (BYOD/COPE)
Healthcare staff phones with potential PHI in messaging apps. Samsung Knox secure wipe for Android, Apple Erase All + Activation Lock check for iPhone; same certification flow on both platforms.
Medical Device Storage
Removable SSD/CF cards in ultrasound, MRI consoles, ECG recorders. PIWIPE clears these media via NIST 800-88 Clear; even resale outside the device vendor poses no PHI risk.
Backup Disk Archive
10-year-old backup HDDs are both cost and breach risk. PIWIPE NIST 800-88 + certificate + cloud archive: backups safely sanitized, records retained for 6 years.
Insurance Carrier (Payer)
Call-center PCs at health insurers process claims and member data. In bulk-inventory mode, hundreds of devices wiped with the same standard — DoD 3-pass + NIST verify — and one-click report.
Sister industry standards: NIST 800-88 · DoD 5220.22-M · GDPR
Compliance Checklist
HIPAA media-disposal audit checklist
A 9-item checklist based on 45 CFR §164.310(d)(2)(i) and HHS guidance. Items PIWIPE directly fulfills are highlighted (✓); items requiring your organizational policy work appear with (◐).
- ✓Written Decommissioning Policy — Align the PHI-media disposal procedure with §164.310. (◐)
- ✓Device Inventory Record — Every PHI-containing device must be inventoried with serial; PIWIPE auto-records on connection.
- ✓NIST 800-88 Standard Application — Select Clear or Purge per device type; PIWIPE auto-recommends.
- ✓Tamper-Proof Certificate — Per-device PDF with SHA-256 hash + PKCS#7 digital signature; PIWIPE default.
- ✓QR-Based Independent Verification — Auditor must be able to verify the certificate without login.
- ✓6-Year Cloud Archive — HIPAA documentation retention; PIWIPE cloud console keeps indefinitely with 6+ year filtering.
- ✓Operator Audit Trail — Which technician, which device, when — captured on certificate and cloud logs.
- ✓Workforce Training Record — Document operator media-disposal training; the operator note field on the certificate can reference this record. (◐)
- ✓Breach Notification Readiness — A wipe certificate documents "low probability of compromise" if a device is lost (45 CFR §164.404).
Frequently Asked
HIPAA & Disk Wipe
Data Residency
Certificate and audit-record control: store on your own server
HIPAA requires that PHI-related components (including certificates) remain under the control of the covered entity or a BAA-signed business associate. Storing your certificate archive on a foreign third-party cloud creates complexity with BAA requirements — and notably with state-level privacy laws (CCPA, NY SHIELD, TX HB 4).
PIWIPE's built-in FTP/SFTP sync writes each certificate to the FTP/SFTP server you specify at the moment it's issued. That server can be your hospital data center, a BAA-covered HIPAA-eligible cloud (AWS HIPAA-eligible, Azure for Healthcare), or your own on-prem infrastructure. Sync to the PIWIPE cloud console is optional; turn it off and certificates never leave your environment. Compare with other vendors →
Sanitize healthcare data, audit-ready.
Contact our team for a tailored demo and pricing for your organization.
Or call us: +90 212 916 12 22